What is Bot and Botnet
Dear Friends,
What is Bot and Botnet
Dear Friends,
How Bots are installed in Computer
Dear Friends,
Feeling of Bots’ Presence
Dear Friends
What is Worm?
Dear Friends,
We have already discussed about the details of Trojan and we will discuss about worm and how it endangers our computer and how we can get rid of from this. So lets start about where from it has come and what it is and how to get relief.
History: - Initially this term was used for good purpose but as the time passes it lost its importance to the world as the computer misusers misused it and changed its nature and character for their personal ill motive. The term "worm" actually comes from a science fiction story called The Shockwave Rider written by John Brunner in 1975. In short, the story is about a totalitarian government that controls its citizens through a powerful computer network. A freedom fighter infests this network with a program called a "tapeworm" forcing the government to shut down the network, thereby destroy its base of power.
But the world was not much aware about that word as it was not known to all but on 2nd November 1988 when Robert Tappan Morris, a Cornell University graduate student and son of Robert Morris, the former chief scientist at the National Computer Security Center, a division of the National Security Agency (NSA), when brought it in the internet from MIT to conceal the fact that it actually originated from Cornell, it became famous (????) to all as it caused near about 6000 to 9000 computer damaged and collapsed the internet but when he realized that it is causing huge harm to the cyber and computer world he then contacting with one of his friend from Harvard send an anonymous message about how to prevent them and how to heal the infected computer from Harvard over the network but as the internet was clogged it was not reached to anyone, which resulted millions of dollar loss. But as per his version he wanted to gauge the measure of internet and how many computers are in touch with internet and even he did not realize at the time of creation that it may cause such huge loss and it is heard that it was programmed in such a way that it would keep continue counting how many computers in the net has got infected. So this is the history.
What actually worm is: - A worm is similar to a virus by design and is considered to be a sub-class of a virus. Worms spread from computer to computer, but unlike a virus, it has the capability to travel without any human action. A worm takes advantage of file or information transport features on your system, which is what allows it to travel unaided.
The biggest danger with a worm is its capability to replicate itself on your system, so rather than your computer sending out a single worm, it could send out hundreds or thousands of copies of itself, creating a huge devastating effect. Many worms come in the form of email file attachments, or as hidden additions to actual email messages, which trigger the execution of infectious code. And even some website contents may carry worm and when you click on them they will try to get installed if you don’t have good antivirus in your system.
Only a good Antivirus can stop and prevent the worm by its background scanning and keep the antivirus always updated.
With Thanks
Urproblemmysolution team
How Trojans enters in your computer.
Dear Friends,
So now you have understood which can stop you from being the victim of Trojan and we think you will follow this during net surfing and installing any file from any outside source.
Urproblemmysolution Team
Pl keep continue your visit www.urproblemmysolution.blogspot.com for knowing more about cyber danger.
What casualty Trojan does in your computer.
Dear Friends,
How we can get rid of Trojans
Dear Friends,
We have discussed so far what is Trojan, history of Trojan, how it comes to you, what it does in your computer and now we will discuss you the last topic about Trojan i.e.: how to get rid of from Trojans. Anti-virus programs detect known Trojan horses. However, Trojan horse programs are easier to create than viruses and many are created in small volumes. These Trojan horse programs will not be detected by anti-virus software. The best defense against a Trojan horse is to never run a program that is sent to you. The others are as follows:-
1) Take back up of your important files and then format it and re-install the system.
2) Install good paid antivirus not the free version.
3) Keep the antivirus in auto scanning mode always.
4) Always allow your antivirus to scan your computer completely.
5) If you download any file or image or film don’t run it until you scanned it by your own good paid antivirus like Kaspersky and Norton. Don’t go against antivirus.
For knowing the recent Trojans you are requested to visit http://en.wikipedia.org/wiki/List_of_trojan_horses
With Thanks
Urproblemmysolution team.
Pl keep continue your visit www.urproblemmysolution.blogspot.com for knowing more about cyber danger.

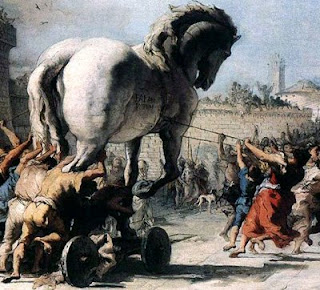
What is The History of Trojan
Dear Friends,
Dear Friends,
Today is our most happiest day for our blog as one of the bset Cyber Security Expert of the World Mr. Gunnar has made his comment on one of our posting on blog and that is on the topic "Pay Pal member beware from phishers and and cyber criminals". This is the most valuable comment of our blog so far and so we have decided to post it on the front page for your kind notice and future guideline. And here it is for you:-
Gunnar said...
Hi there,
I am a friend of Sitanshu Ray who forwarded me that link of your interesting blog.
Phishing mails like this will never stop in a principal way and of cause they can be danger like in this case.
This Phishing mail you posted looks like an "invitation" of a (so called) drive-by-infection. This means, if you open the link from this mail, your computer might get infected by a virus/trojan in a second without interaction. They might use unfixed or new vulnerabiliys in the browser and/or plugins to do that and its very possible that your antivirus didnt "know" that used virus/trojan. In worst case, your computer is after this a part of a botnet or they "only" steal data out of your computer like passwords, banking data etc.
If you check the main URL of this like, you will see that the owner of the domain is "inContact Inc." - a call center. Call Center often act like this and offer there service to "normal" companys i.e. to send out spam etc.
On the inContact Website you can also see the address of them: 7730 South Union Park Avenue, Suite 500 Salt Lake City, UT 84047 or check the nic.com with the whois data.
But the problem is: It's hard to attest them, that they send the phishing mail by themself. They can easily say someone (unknown) did it. But there are also some possibility to make traps for them that could it be possible to sue them ... ;-)
Kind regards
Gunnar
July 22, 2009 10:16 AM
Pay Pal Members Beware From Phishers and Cyber criminals
Dear Friends,
Now we are producing before you about latest fraud emails which was seemed to be generated from Pay Pal and it came to one of our team member and then feeling it suspicious he mailed the entire content to Pay Pal and in response what Pay Pal said we are producing that before you for your future reference.
Here is the suspected mail from spammer with its header file which was sent to Pay Pal for verification:-
Form MessageDear Kept Hidden ,( Here they used the name, which they did not use in previous mail)
On ##/##/#### I replied to the email message you sent regarding your
>http://surveys#.incontact.com/paypal/survey_paypal.taf?survey_id=####'
Here is the response from Pay Pal about the above email:-
Dear Name Kept hidden,
Thank you for contacting PayPal.
Hello, my name is Hazel. From reading your email, I know you are
concerned about the suspicious email you received. I'm sorry if this
caused you any trouble, I'll be glad to explain this further for you.
Thank you for submitting this suspicious email, Mr. Hidden. We did
not send it, so please don't click any link in the email and delete it
if you haven't already. We also recommend that you log in to your PayPal
account and check your transaction history for any inaccuracies.
Please forward the original email to spoof@paypal.com and then delete
the email from your mailbox. Never click any links or attachments in a
suspicious email.
The majority of Unauthorized Access cases are a result of inadvertently
providing account information, such as bank or credit card account
numbers on a 'fake' PayPal website or in response to a 'fake' PayPal
email.
It is also possible that if you have other accounts (email, eBay, etc.)
that share the same password as your PayPal account, and one of those
accounts was compromised, your PayPal account can be at risk of being
compromised as well.
Remember these steps to help protect your PayPal account from
Unauthorized Account Access:
Emails - Make sure they are sent from PayPal
1. If you receive an email and are unsure whether it is from PayPal,
open a new web browser (e.g., Internet Explorer or Netscape) and go to
the PayPal website. Don't click on any link in an email which seems
suspicious to you.
2. Some spoof websites will send emails that pretend to come from
PayPal to entice you to log in at the spoof URL. Be extremely cautious
of emails that direct you to a website that asks for your information,
such as your bank or credit card account numbers.
3. Stay safe; don't respond to emails asking for any of the
following:
o Your password and email address combination
o Credit card numbers
o Bank account numbers
o Social security numbers
o Drivers license number
o First and Last Names
Email Greeting -
PayPal will never send you an email with the greeting "Dear PayPal User"
or "Dear PayPal Member." Emails initiated by PayPal will address you by
your first and last name, or the business name associated with your
PayPal account. Please note that the automatic response you get from us
may not address you by name.
Always log into the PayPal site
* PayPal will only ask for information after you have securely
logged in.
* For your security, PayPal will never ask you to re-enter your full
bank account, credit, or debit card number without providing you at
least the last two digits of the number. These digits let you know that
we already know the full number and are asking you for the rest of it.
Beware of any website or email asking for these numbers for
"verification" that does not prove that it knows the number by providing
at least the last two digits.
Website pages - make sure that they are hosted by PayPal
1. When using the PayPal service, always make sure the PayPal url
address listed at the top of the browser begins with "https." The "s"
ensures that the website is secure. Even if the URL contains the word
"PayPal" it may not be a PayPal webpage.
2. Look for the '"lock" symbol that appears in the lower right hand
corner of the browser. This symbol indicates that it is a secure site.
Do not download attachments, software updates, or any application to
your computer via a link you received in an email. PayPal will not ask
you to download anything for your account to work.
Passwords - keep it on PayPal
1. Use a unique password for the PayPal account and change it every
30-60 days.
2. The password should be one that is not used on any other site,
service, or login.
Thanks for sharing your concerns with us. We value what you have to say,
and we know situations like this can be difficult. If you have more
questions, visit our Help Center by clicking "Help" in the top right
corner of any PayPal page.
Sincerely,
Hazel
PayPal, an eBay Company
Copyright© 2009 PayPal Inc. All rights reserved.
Consumer advisory: PayPal Pte Ltd, the Holder of the PayPal™ payment
service stored value facility, does not require the approval of the
Monetary Authority of Singapore. Consumers (users) are advised to read
the terms and conditions carefully.
Pay Pal Members Beware From Phishers and Cyber criminals
Dear Friends,
Now we are producing before you about two fraud emails which was seemed to be generated from Pay Pal and it came to one of our team member and then feeling it suspicious he mailed the entire content to Pay Pal and in response what Pay Pal said we are producing that before you for your future reference.
Here is the suspected mail from spammer with its header file which was sent to Pay Pal for verification:-
Form Message
customer subject: English
customer message: Additional Information: 'I received this mai on
##/##/#### and was it from yours?
"Dear PayPal member,
We're sorry. We are not able to process your recent reply to our email.
We are the processor for the email surveys for PayPal and are not
directly linked to the PayPal customer service center.
Please respond through the survey link imbedded in the original email
you received from us.
Thank you and we apologize for the inconvenience.
PayPal Survey Partner"
This is the header:-
Delivered-To: kept hidden##@gmail.com
>Received: by 10.115.60.18 with SMTP id n##cs######wak;
> Mon, ## Jul #### ##:##:## -#### (PDT)
>Received: by 10.140.203.3 with SMTP id
a#mr#######rvg.###.#############;
> Mon, ## Jul #### ##:##:## -#### (PDT)
>Return-Path: <>
>Received: from mail.benchmarkportal.com (mail.echosurvey.com
[###.###.##.###])
> by mx.google.com with ESMTP id
##si########pzk.###.####.##.##.##.##.##;
> Mon, ## Jul #### ##:##:## -#### (PDT)
>Received-SPF: neutral (google.com: 207.166.99.104 is neither permitted
nor denied by best guess record for domain of mail.benchmarkportal.com)
client-ip=###.###.##.###;
>Authentication-Results: mx.google.com; spf=neutral (google.com:
207.166.99.104 is neither permitted nor denied by best guess record for
domain of mail.benchmarkportal.com) smtp.mail=
>precedence: bulk
>in-reply-to: 94dd4f4c0907201044pa3ba0ct@mail.gmail.com
>return-path: <>
>Date: Mon, ## Jul #### ##:##:## -####
>Message-Id:
>from: "paypal.feedback"
>to:
>subject: Automatic Response'
Now what Pay Pal replied:-
Dear Name Kept hidden,
Thank you for contacting PayPal.
Hi Kept hidden! I have read your email and understand your concern over the
email you received. Let me assist you further.
If you think the email you received did not match the description I have
included below please forward the email you received to
'spoof@paypal.com'.
PayPal frequently issues surveys in attempt to find more ways to improve
our service and accommodate your needs.
* If you receive a survey from PayPal, or a third party vendor on
behalf of PayPal, it will arrive as a link sent to you through email *
* To get to the survey page, simply click on the link, or paste the
link into your browser's web address box
Please keep in mind that a medium like email allows anyone to send a
message to you. Before entering information into the survey you received
via email, you should verify the source of the email.
* To make sure that the email survey you received was from PayPal,
follow these tips:
1. You will NOT need to enter your password at any point during the
survey
2. The survey you received will never ask you for any personal
information
3. All surveys will address you by first and last name
We appreciate your input, and we thank you for using PayPal!
We know situations like this can be difficult, so thanks for working
with us. If you have more questions, visit our Help Center by clicking
"Help" in the top right corner of any PayPal page.
Sincerely,
A Name is there
PayPal, an eBay Company
Copyright © 1999-2009 PayPal. All rights reserved.
Consumer advisory - PayPal Pte. Ltd., the holder of PayPal's stored
value facility, does not require the approval of the Monetary Authority
of Singapore. Users are advised to read the terms and conditions
carefully.
How To Keep Your Pay Pal Account More Safe?
Dear Friends,
One of our reader has given his valuable command over Pay Pal Account Security and it seemed to us that it should post on our blog so that our other readers get some more knowledge about their security tips for Pay Pal and we will suggest you to read our previous posting first and this is the continuation of that discussion and we think this will help you to keep your Pay Pal Account more and more safe from hacking or money loss.
Thanks
Here is the valuable comment of Kailash.
All About Opensource said...
"I would like to say thanks to all well wishers of this site and also Urproblemmysolution Team for maintaining a such a informative site.
In this post Urproblemmysolution Team almost cover all the things regarding paypal, though i just need to add few point like when ever trying paying something via paypal for any kind of subscription with multiple payment term please do not check the options like "Auto renewal" or "Auto recharge" or "auto payment option" .
Before paying or receiving any money in paypal please read T&C carefully that will take few min for first time but those few min can save your $$$$ being fraud by some cracker.
Keep Changing your paypal password in every 7 days or even after every two transaction.
FYI the official site of Paypal is www.paypal.com
p.s. On-Screen Keyboard can be accessible by type "osk" on "Run"
Cheers :) !!!
Kailash"
What is Pay Pal (www.paypal.com) Account?
Dear Friends,
As per our words and promise we are going to discuss you about Pay Pal as this is the safest e-transactions in the world as if you visit the above noted website you will find it starts with “https” if you use normal browser and don't use faster browser and for that all the data passes through it to their server is in encrypted form. So we think we first introduce you what is Pay Pal. This is basically a mediator between you and the e-seller and for that they don’t charge any fees from you but they charge it from the seller and that is also a small percentage on sales value. Before that you will have to have an account with them. For opening the account you just need a valid email id, name and address, a valid telephone number. So now a question will arise in your mind that just with the help of that email id can I purchase anything from e-marketing? What should be your answer is it possible that you don’t have money in your account and you will purchase anything. So what you should do. You should keep a balance in your Pay Pal Account and from there you will spend and Pay Pal is taking responsibility to pay the amount to your seller where you don’t know seller directly but getting his product.
So in this stage a question may arise in your mind the why I will do so, I have credit card and debit card facility and I can purchase it by using those from net. Yes you can do that but mind it that all the net transactions are not done through secured channel. Some of them are unsecured and their there is every possibility of your credit card and debit card number get hacked and the hacker may misuse it and for that Pay Pal business is in boom. In our first part we discussed that a balance is needed in your Pay Pal Account and you can’t deposit money directly in your Pay Pal Account from out site the USA as the business is run from USA and for that you will have to transfer the balance to your Pay Pal Account from your credit card or some other cards as desired by Pay Pal. Only the American citizens can do the bank transfer and if you don’t have your credit card there is option to transfer the amount from your friend’s card also if your friend wants and for that I made a quarry to Pay Pal authority that why this system is continued by them and why the other countries don’t have the facility of bank transfer and in response they told that it is due to the security purpose and if a card is used the verification of person is possible and at the time of final transaction before purchase they use their Gausebeck-Levchin Test ( which we discussed earlier) for avoiding bot transaction and even I tried to access their site by using a proxy server but they denied. So you can say that it is secured.
We think now you have become angry on us and your anger is reaching in such a position that you will tell me then why you have posted this here if the system is so secured and you promised us that you will tell us the danger side of cyber world. Yes you are right that the system is very much secured but in spite of that the Pay Pal accounts are get hacked and the people are becoming victim over this and that is why we were discussing you the details of Pay Pal account system. In our next posting we will discuss you what are the dangers in Pay Pal account and why and how we can get rid of from there. So keep in touch with us.
Thanks
What is Gausebeck-Levchin Test?
Dear Friends,
So a question may arise in your mind that what is CAPTCHA test? CAPTCHA test is the abbreviated form of Completely Automated Public Turing Test to Tell Computers and Humans Apart. Actually it is a human verification test. When you enter in a yahoo chat room you find a box where few words are written in a typical manner and you have to put those words in the box below and if it matches then you get the permission to enter into the room and allow chatting. So you will ask why this is needed. This is needed as spammers may enter in the room for advertising their site by using “bot” programming and the spammers can’t pass the CAPTCHA test so the chatting personalities present must be there and there IP addresses will be tracked for future references.
We think this will help you in future and keep in mind before doing cyber crime where the CAPTCHA test exists.
Thank You
Important Tips For Cyber Café Users
Dear Friends,
We promised in our last posting that we will post some important tips for those who use cyber cafes for their net surfing. We believe that this will be helpful to all of you as most of all have to use cyber cafes for any urgent situation. So please read this and try to follow in your life.
| Very important tips when using Public Terminals and Cyber Cafes |
| ||
| | | | |
| | | Tip 1 E-Bay Users - Watch Out Don't walk away while logged in. Many web sites let you log in, but set cookies for an online session (such as eBay) so if you close the browser and reopen it, you don't have to re-logon. If you just close the browser and walk away, the next user (who may have been watching while you were surfing), could pickup where you left off. Be especially careful using a Microsoft Passport account as well, since it can also be persistent. | |
| | | Tip 2 Surfing at an Internet Cafe, the Public Library, Terminal at the Hotel, or any Terminal Accessible to Others - Watch Out 1. If you use a public terminal (e.g., Internet cafe) with a Windows XP installation, it could ask if you want to associate your passport account to the Windows XP account. Be sure to say "no"(we repeat, SAY "NO") if you get this prompt, or you'll be giving your passport account to everyone that uses that machine. 2. Normal surfing leaves an electronic trail of temporary files, cookies and a history of where you've been. When you're done with surfing, if you're using: · Internet Explorer, click on Tools and Internet Options, on the · General tab, click on Delete Cookies, Delete Files (and be sure Offline content is checked), and · Clear History. · If you downloaded any documents, delete them as well. If you edited any documents clear the "recently used documents" list. To this with Windows XP · right click on the taskbar at the bottom of the screen and then, · select Properties, · select the Start Menu Tab, and · click on Customize then · Advanced. On the Advanced tab, click on the · Clear List button for Recent Documents. | |
|
| | Tip 3 Restrict Pop-Up Windows and Cookies Pop-up windows are often generated by some kind of scripting or active content. Adjusting the settings within one's browser can reduce or even prevent scripting or active content. In turn, the number of pop-up windows that appear will be reduced. Some browsers offer a specific option to block or limit pop-up windows. Accessing Web-based E-Mail Accounts When connecting to a Web-based mail account via a cyber café (e.g., Yahoo!, gmail.com), for instance, do as follows: 1) Start the program Microsoft Notepad or Word or any word processing program installed and type your · User Name, · Password, then · Copy the user name AND password using Control C and then paste both into the appropriate fields (use CTRL V) when wanting to log into your web-based e-mail account The above procedure prevents Keyloggers or password stealers program from grabbing your username and password when trying to log-on from such a public terminal - The same logic applies if you log into a web site from your own computer. – 2) Refuse the option that may pop-up by the browser to save the password. 3) Use the site's log off option (disconnect, or close session option), in turn, this will prevent the next user at the cyber café from being able to access your account. 4) Exit the browser and then open it again before leaving the computer to the next user. These types of precautions should be taken because a lot of mail systems use cookies via Internet to maintain the session open while the user goes back and forth between Web pages. Thus, user names and passwords don't have to be requested constantly. Cookies store a value that means "open" to the current session and user, so if the session is not disconnected, anyone can use it. This is especially dangerous in cyber cafés, where several different users continuously work on the same computer, one after another. Thanks Urproblemmysolution Team | |
How Cookie works
Hallo Friends,
Now you will ask us that in your last posting you discussed us that cookies are not computer programs so how will they work and how can they work and yes you are right its not a computer Program and nor a virus but in spite of that it works and how it works. Actually it works as a passive worker that means when it stays in your computer it helps the browser and server to work freely and smoothly. In our last posting we discussed about the types of cookies and if you read about that then this posting will help you to understand this topic.
The manner through which cookie moves data
· If you type the URL of a Web site into your browser, your browser sends a request to the Web site for the page. For example, if you type the URL http://www.google.com into your browser, your browser will contact Google's server and request its home page.
· When the browser does this, it will look on your machine for a cookie file that Google has set. If it finds an Google cookie file, your browser will send all of the name-value pairs in the file to Google's server along with the URL. If it finds no cookie file, it will send no cookie data.
· Google's Web server receives the cookie data and the request for a page. If name-value pairs are received, Google can use them.
· If no name-value pairs are received, Google knows that you have not visited before. The server creates a new ID for you in Google's database and then sends name-value pairs to your machine in the header for the web page it sends. Your machine stores the name-value pairs on your hard disk.
· The Web server can change name-value pairs or add new pairs whenever you visit the site and request a page.
There are other pieces of information that the server can send with the name-value pair. One of these is an expiration date. Another is a path (so that the site can associate different cookie values with different parts of the site).
You have control over this process. You can set an option in your browser so that the browser informs you every time a site sends name-value pairs to you. You can then accept or deny the values. (source howstaffworks)
Thanks
Urproblemmysolution Team
Dear Friends,
If you read about what cookies are then you will get there that Cookies can contain specific information about the user:
So your user name and password of a visiting site may be stored in your computer cookie of that site and you think someone has stolen it by using some software so is it vulnerable or not? You think it. So we need some general solution.
How can one describe the solution from cookies?
To increase your level of security, adjust your privacy and security settings to block or limit cookies in your web browser as follows:
If you don’t use Firefox please go to options in your browser and do the same thing as discussed above.
In our next posting we will give the Very important tips when using Public Terminals and Cyber Cafes please keep visit this blog for your future help.
Urproblemmysolution Team